Single Sign-On in Okta service
Okta.com offers SAML2.0 SSO standard so LiquidFiles appliance can use its authentication service and login your Okta users.
Settings in Okta
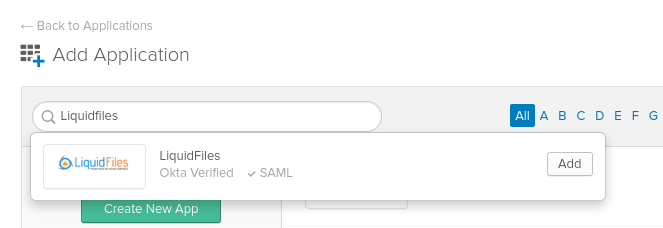
Log in with your account to your okta.com admin web GUI. Okta team has preconfigured application for LiquidFiles appliance so most of configuration work have been already done. Click on Applications → Add Application button. Search liquidfiles and add the app.
Fill in Base URL of your LiquidFiles server.

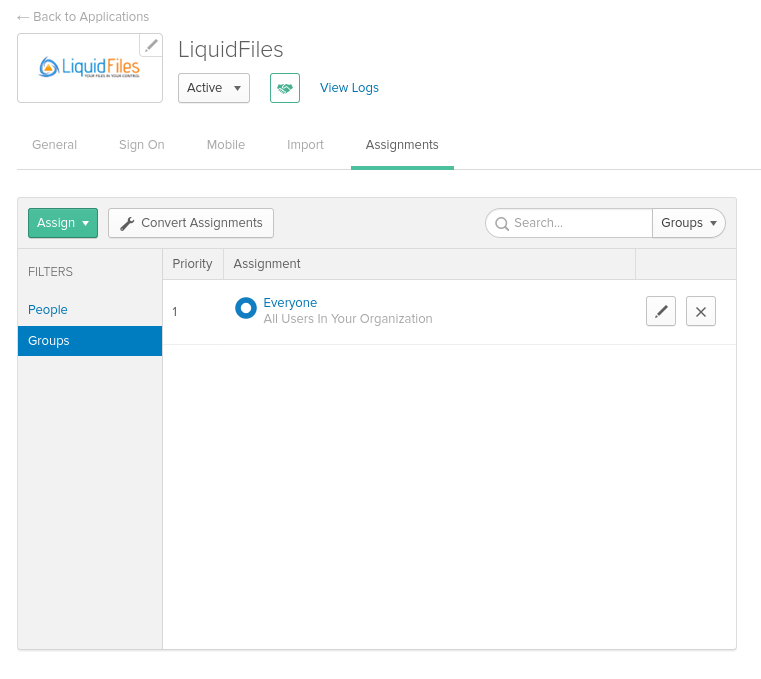
When done then under the Assignments tab assign people, or whole users groups who should be able SSO login to the LF server
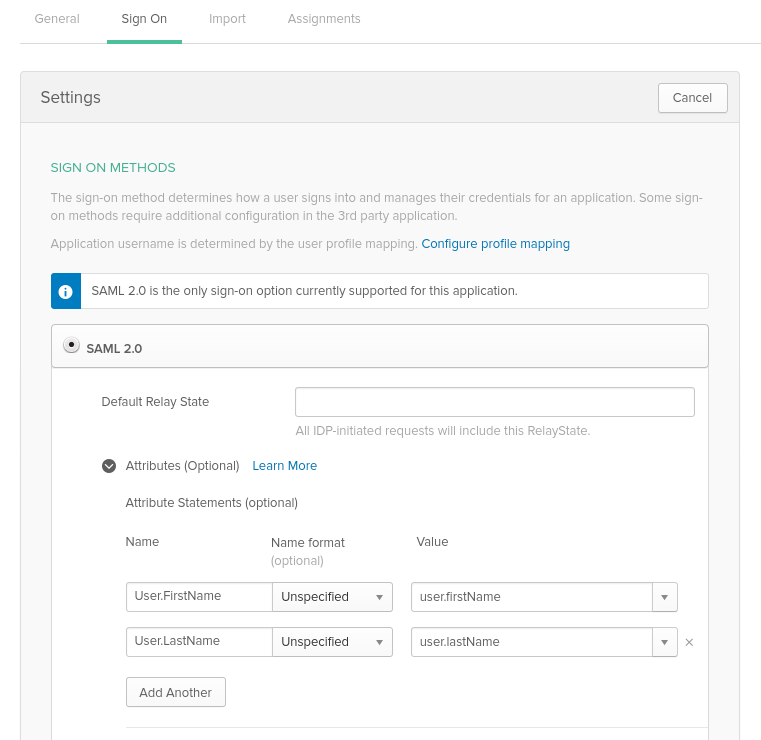
Switch to the Sign On tab and edit that settings page, then scroll down and click on the Attributes (Optional) arrow.
In this part we will need to map Otka user's first and last name attributes to the SAML response so the LF server can pick them up. Okta's user.firstName and user.lastname is mapped to SAML's User.FirstName and User.LastName attributes as displayed on the following screenshot. Please note attributes are Case Sensitive.
When all set save the configuration.
Still under the Sign On tab click on the View Setup Instruction button to display: IdP Login URL, IdP Logout URL, IdP Cert FingerPrint, Signature Algorithm settings which Okta generated exactly for your LF server.
Or alternatively open this Okta's configuration howto link directly here.
Settings in LiquidFiles
Now login on your LF server and open the Admin → Configuration → Single Sign-On (SSO) configuration page where copy/paste the generated settings one by one.
- Single Sign On Method: SAML 2
- IdP Login URL: https://yourdomain.okta.com/app/liquidfiles/1234abcd/sso/saml
- IdP Logout URL: https://yourdomain.okta.com (or https://liquidfiles.domain.com)
- IdP Cert Fingerprint: generated SHA-256 fingerpring of the signing certificate
- Name Identifier: urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress (default settings)
- Authn Context: urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport (default settings)
- Signature Algorithm: SHA-256
- Auth Comparsion: Minimum
